The music industry wants to build web3. But can they secure it?
Your DAO is a democracy... if you can keep it.
In 2021, we saw the rise of NFTs—putting merchandise and music royalties on the blockchain. But many of those NFTs were sold or auctioned by traditional corporations like Monstercat or Royalty Exchange. These NFTs were on the blockchain, but the surrounding ecosystem was not.
Over the past few years, activists and founders have been building momentum for web3—which would put everything on the blockchain by replacing those corporations with decentralized autonomous organizations (DAOs).
A web3-powered music industry is a compelling vision—especially if it is fairer to artists. But there are two reasons to remain skeptical:
Necessity. It is not clear if web3 is necessary for building better music businesses. Perhaps we can achieve the same goals with web2.
Security. DAOs must be designed with careful consideration to security, or they’ll be robbed of all assets in their custody. Right now, almost nobody is being careful enough.
(Please note my ethical disclosures listed at the end of this piece.)
When are blockchains and DAOs necessary?
Blockchains offer an important security guarantee: counterfeiting a transaction is incredibly difficult (but not impossible).
So, blockchains are useful for implementing products that need strong resistance to counterfeiting, such as:
The GET Protocol. GET makes it possible to sell tickets for concerts and live events as NFTs—preventing ticket counterfeiting.
Ethereum Name Service (ENS). Traditional website domain names (like jamesmishra.com) are governed by the notoriously insecure DNS protocol. ENS implements blockchain-based domain names (like jamesmishra.eth) with resistance to the vulnerabilities that have plagued DNS for decades.
But the recorded music industry is different. During the 2000s, the music industry tried and failed to stop piracy/counterfeiting with cryptographic digital rights management (DRM) systems1. But during the 2010s, the rise of music streaming proved that anti-counterfeiting tech wasn’t the path to higher revenues—building a more user-friendly product was2.
Similarly, if you want to start a record label or streaming site that is fairer to listeners and artists, you don’t need a DAO or any anti-counterfeiting tech. You can build any traditional “web2” company with whatever user experience and economics you want.
DAOs present unsolved security challenges
Attackers have an enormous financial motivation to attack DAOs—they’re full of pseudoanonymous money. We still know very little about how DAOs can be attacked, but there are three notable categories of attacks:
1. Attacks exploiting transparency
Most blockchains are public places where anybody can see the actions of the other participants. A DAO’s transparency can be exploited in several ways:
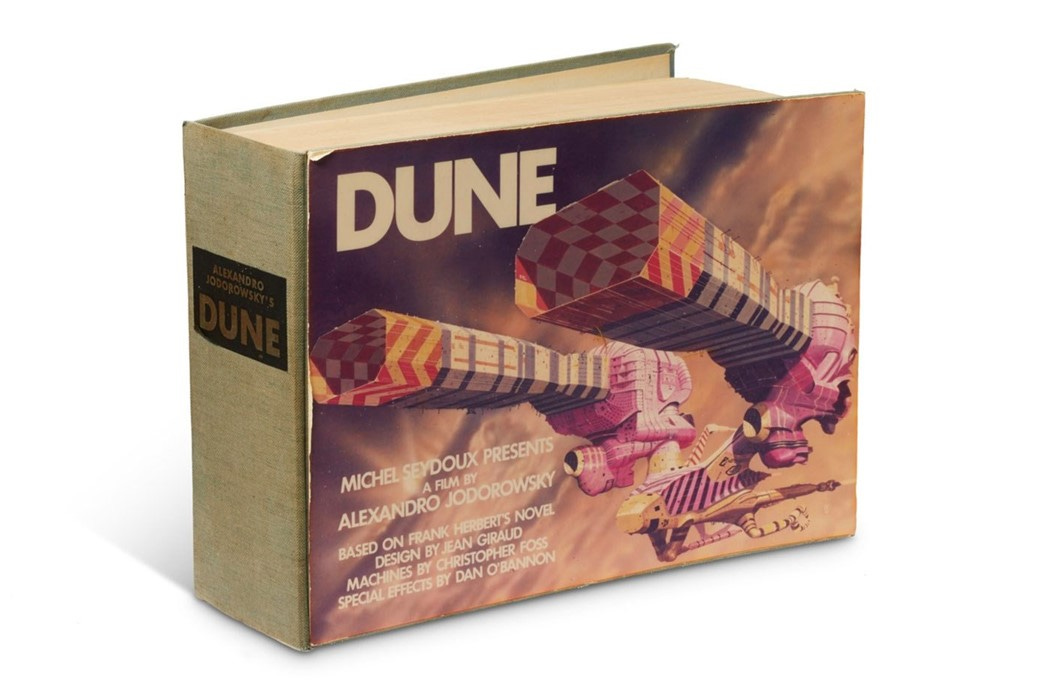
Adversarial bidding. Many DAOs’ balance sheet is publicly visible on the blockchain, which compromises them when they bid for an asset at an auction. Citadel CEO Ken Griffin may have defeated ConstitutionDAO by pricing his winning bid barely above their war chest. On the other hand, SpiceDAO won their auction for a rare book—but they paid 100x the book’s estimated value. Someone may have priced a bid just under SpiceDAO’s war chest so the book’s seller would make more money.
Front-running against decentralized exchanges. Decentralized exchanges on certain blockchains3 may be vulnerable to front-running attacks. When a victim submits a trade to the exchange, an attacker can spot the underlying unconfirmed transaction in the blockchain’s mempool. The attacker can submit a competing trade, paying a higher fee so it gets confirmed before the victim’s trade. The attacker’s trade returns a guaranteed profit, and the victim’s trade suffers from price slippage.
We could prevent transparency attacks by using zero-knowledge proofs—a cryptographic method for proving a statement about a piece of information without leaking the information itself. For example, the Tornado Cash DApp and the Monero and Zcash blockchains use zero-knowledge proofs to implement untraceable transactions.
2. Attacks against smart contracts
A DAO’s policies—from treasury to voting rights—are implemented by smart contracts, which are programs that run on a blockchain’s validator nodes.
Smart contracts are incredibly difficult to write without security flaws. In 2021, over $2.6 billion of assets were lost to smart contract hacks and similar vulnerabilities4.

Some notable hacks from the past several years include:
The first DAO. “The DAO” was a decentralized venture capital firm launched on Ethereum in April 2016. A few weeks later, an attacker used vulnerabilities in The DAO’s smart contracts to withdraw5 3.5 million ether—worth roughly $50 million at the time—until most of the Ethereum community reversed the hack with a controversial hard fork.
Parity Multi-signature Wallet. In July 2017, an attacker stole over $30 million of assets from three customers of Parity’s smart contract wallet. Parity responded with a new version of their smart contract, fixing the vulnerability and adding an emergency “kill switch” to prevent withdrawals in case a new vulnerability was discovered. But the kill switch itself had a vulnerability, which someone exploited in November 2017 to freeze over $150 million of assets across 587 Parity customer wallets.
Poly Network. In August 2021, a hacker stole $610 million of cryptoassets from Poly Network. This was the largest known smart contract hack in history… until he returned all of the stolen assets over the following two weeks.
Nowadays, security engineers and automated scanners are getting better at reading a smart contract and finding vulnerabilities. But many vulnerabilities are mathematically impossible6 to discover this way.
To find those vulnerabilities, we’d have to run the contract exactly as an attacker would7. And that is a losing battle too, because you and I are outnumbered by our enemies.
3. Attacks against governance
Many DAOs decentralize their decision-making by issuing governance tokens—which can offer both voting rights and financial incentives.
But democracy and capitalism tend to undermine each other, and when this happens, DAOs can be vulnerable to governance attacks.

Last November, the blockchain lending project Mochi Inu attempted a governance attack against the decentralized exchange Curve Finance. The details are complicated, but broadly:
Curve uses their CRV governance token to reward people who deposit cryptoassets into Curve’s liquidity pools. CRV holders can vote to change how Curve distributes rewards.
Mochi attracted $150 million8 of other people’s cryptoassets to Mochi’s pool on Curve.
Using their $150 million pool as collateral9, Mochi issued themselves a $46 million loan10 to purchase CVX tokens11—which offer Curve’s CRV rewards and voting rights by proxy.
With enough CVX, Mochi could vote for Curve to pay higher rewards to Mochi’s pool. Higher rewards lead to more voting rights, creating a cycle that could have allowed Mochi to ransack Curve’s reward schemes.
Curve’s leadership stopped the attack by enabling their “Emergency DAO”—a nine-member committee that manually disabled Mochi’s ability to receive CRV rewards. While the Emergency DAO was successful, some people [a,b,c,d,e] raised concerns that it was too centralized—making it vulnerable to political corruption or attack12.
As a final note, Mochi’s tactics failed, but their fundraising machine was terrifying. In the near future, pseudonymous attackers will raise hundreds of millions of dollars to fund sophisticated and devastating attacks.
Conclusion
From studying the above attacks, we learn two things:
1. Blockchains and DAOs are so new, we don’t understand them

Because blockchains are so new, we know very little about breaking them. Researchers can take decades to find a vulnerability. For example, the relatively simple SHA-1 algorithm was studied for twenty-two years13 before it was publicly broken in 2017.
Our adversaries could find vulnerabilities decades before us. For example, differential cryptanalysis attacks were publicly discovered in 1990, but the US National Security Agency (NSA) secretly knew about (and may have weaponized) the attacks at least sixteen years earlier14.
2. For the music industry, web2 might be more secure
If your DAO is hacked, it is often both devastating and irreversible. The attacker could have your assets, voting rights, and be able to change contracts and policies. Undoing the hack is about as difficult as counterfeiting a transaction—and for the same reason.
On the other hand, you can steal money or data from a “web2” music business—but it’s almost impossible for a hacker to control contracts or governance. Hacking Spotify won’t put you on their Board of Directors. Hacking Universal Music Group won’t make Taylor Swift renegotiate her contract with you.
The web3 activists have a vision of a music industry that is fairer to artists. And it’s a great vision! But fairness is something we can build anywhere—even in web2.
Ethical disclosures
My investments and past employers may influence my writing about blockchains, cryptography, and the music industry:
In 2014, I completed a summer internship with the US National Security Agency. Nothing in this essay relates to my work with the NSA or my knowledge of their activities. I don’t know anything about differential cryptanalysis.
In 2015, I completed a spring internship with the US Department of Energy’s Oak Ridge National Laboratory (ORNL). My job was to look for vulnerabilities in the Bitcoin protocol that a theoretical quantum computer could exploit. I did not find anything worth publishing.
At this time of writing, I own Bitcoin, Ethereum, Solana, and STREAM. I have previously sold the ENS DAO governance tokens earned from registering two ENS domain names.
Changelog
February 13, 2021: Added a footnote about Curve’s Emergency DAO.
Thanks to CD sales, the US recorded music industry earned record-breaking revenues during the 1980s and 1990s. But because CDs were unencrypted, anybody could upload a flawless copy to a filesharing site—leading to a collapse in industry revenues. In the early 2000s, rightsholders and retailers tried to stop piracy by implementing cryptographic DRM systems like Apple FairPlay and Microsoft Windows Media DRM. But no matter how hard they tried, they couldn’t stop hackers from breaking DRM open [a,b,c,d]. The industry gradually abandoned DRM for downloads starting in the late 2000s; Apple’s iTunes began selling DRM-free downloads from the major labels in April 2009. The rise of music streaming in the early 2010s was the final nail in the coffin for DRM-protected downloads and the music stores that sold them.
Technically, DRM isn’t gone. Many music and video streaming sites protect their streams with cryptographic DRM systems like Apple FairPlay Streaming or Google Widevine. But this technical detail does little to change the successful economics of streaming.
Some blockchain protocols make front-running difficult to impossible. They may not have a mempool or they prevent unconfirmed transactions from skipping in line. The Solana blockchain does both: their Gulf Stream protocol validates transactions without a publicly-visible mempool, and their Proof of History algorithm enforces the ordering of transactions.
This dataset comes from the bug bounty platform Immunefi. The $2.6 billion sum includes lost assets that were later recovered, such as the $600 million stolen from Poly Network and later returned. It also counts the hacks of blockchain protocols not implemented as smart contracts.
The attacker did not immediately gain the stolen funds because of a 28-day waiting period imposed on the withdrawal.
Here is an example: a computer program can run in an infinite loop or it can eventually exit. It is useful to analyze whether a program will run forever… without actually running it and waiting forever. But in 1936, Alan Turing proved that no analysis method could be correct over all possible programs. More precisely: the Halting Problem is mathematically undecidable. For certain vulnerabilities, we can prove that discovering them in all possible smart contracts is at least as undecidable as the Halting Problem.
This seems like a good solution. When we want to find vulnerabilities in a computer program, we don’t just read it; we run it and see what happens. But you couldn’t solve the Halting Problem this way without literally infinite time. Similarly, you might need infinite time to prove a smart contract does not have a vulnerability. But if it does, an attacker might be able to exploit the vulnerability in finite time.
I report Mochi’s liquidity pool as having $150 million in total value locked (TVL) because that is what Llama Airforce’s graphs showed right before the attack. A few publications reported Mochi’s pool at $170 million TVL because that was a higher peak from slightly before the attack started. However, Curve’s leadership and most publications reported the pool TVL as closer to $100 million.
Mochi advertises that loans on their protocol are overcollateralized—including the $46 million loan they borrowed to finance their governance attack. But Curve’s leadership and other community members raised concerns that Mochi was undercollateralized—especially after the attack had started.
It took several steps for Mochi to end up with the CVX tokens. First, Mochi announced MOCHI, their newly-announced governance token, and minted one quadrillion tokens—giving the token a market cap in the billions of dollars. Then, Mochi staked some of their MOCHI to mint $46 million of USDM—their stablecoin that denominates the loans in their protocol. Finally, they executed a series of swaps on exchanges from USDM→DAI→ETH→CVX and vote-locked the CVX.
CVX is the governance token of Convex Finance—a decentralized finance project that makes it easier to earn the Curve protocol’s CRV financial rewards and voting rights.
Many community members defended the Curve Emergency DAO’s actions because Curve’s main DAO can vote to revert any action taken by the Emergency DAO. As per Curve’s leadership, the purpose of the Emergency DAO is to act quickly—not to take away the governing power of the main DAO. But for an attacker’s purposes, being able to hijack the Emergency DAO could potentially be very profitable—even if the attack is not permanent.
SHA-1 was published as a US NIST FIPS standard in 1995. Ten years later, researchers published the first theoretical attacks. In 2015, the first attack against SHA-1 was practically demonstrated on real computers, but it was too limited for real-world attackers to use. SHA-1 was finally broken in 2017 when CWI Amsterdam and Google researchers demonstrated a SHA-1 collision attack by creating two PDF documents with the same SHA-1 hash. This attack is highly dangerous; it can break software programs that use SHA-1 to verify the integrity of digital signatures and files.
A team of researchers at IBM discovered differential cryptanalysis attacks in 1974 when designing the DES encryption algorithm. IBM informed the NSA of their discovery, and the NSA ordered that it be kept secret to preserve the NSA’s cryptographic advantage against their adversaries. That’s all we know for certain. Steven Levy’s book Crypto (starting from page 55) rumors that the NSA already knew about differential cryptanalysis before IBM’s discovery—and that the NSA may have weaponized it. The world learned about differential cryptanalysis when the academic cryptographers Eli Biham and Adi Shamir published their discovery of differential cryptanalysis in 1990. But IBM and the NSA’s earlier discovery remained a secret until 1994, when IBM researcher Don Coppersmith published a paper revealing the story.

